Interface AccelMgr
-
- All Superinterfaces:
Manageable
- All Known Implementing Classes:
AccelMgrImpl
public interface AccelMgr extends Manageable
This object is a Policy Enforcement Point (PEP) using the OpenLDAP Accelerator Policy Decision Point (PDP) on objects that are provisioned RBAC entities that reside in LDAP directory. These APIs map directly to similar named APIs specified by ANSI and NIST RBAC system functions. Many of the java doc function descriptions found below were taken directly from ANSI INCITS 359-2004. The RBAC Functional specification describes administrative operations for the creation and maintenance of RBAC element sets and relations; administrative review functions for performing administrative queries; and system functions for creating and managing RBAC attributes on user sessions and making access control decisions.RBAC0 - Core
Many-to-many relationship between Users, Roles and Permissions. Selective role activation into sessions. API to add, update, delete identity data and perform identity and access control decisions during runtime operations.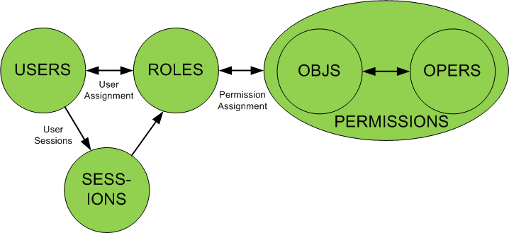
RBAC1 - General Hierarchical Roles
Simplifies role engineering tasks using inheritance of one or more parent roles.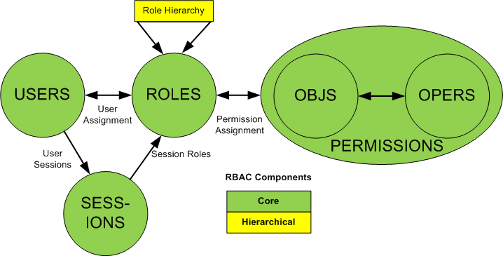
RBAC2 - Static Separation of Duty (SSD) Relations
Enforce mutual membership exclusions across role assignments. Facilitate dual control policies by restricting which roles may be assigned to users in combination. SSD provide added granularity for authorization limits which help enterprises meet strict compliance regulations.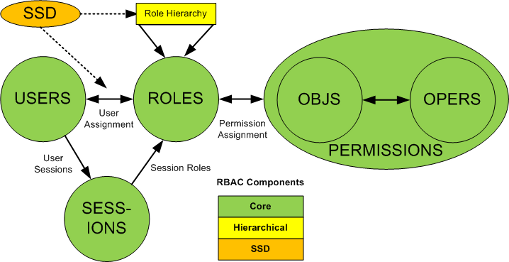
RBAC3 - Dynamic Separation of Duty (DSD) Relations
Control allowed role combinations to be activated within an RBAC session. DSD policies fine tune role policies that facilitate authorization dual control and two man policy restrictions during runtime security checks.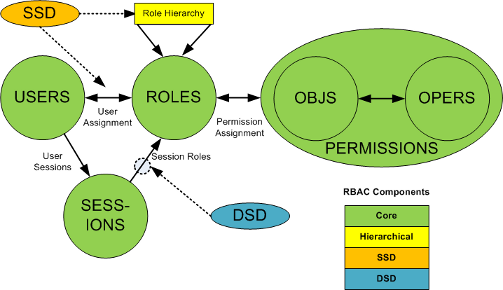
This interface's implementer will NOT be thread safe if parent instance variables (
Manageable.setContextId(String)orManageable.setAdmin(org.apache.directory.fortress.core.model.Session)) are set.- Author:
- Apache Directory Project
-
-
Method Summary
All Methods Instance Methods Abstract Methods Modifier and Type Method Description voidaddActiveRole(Session session, UserRole role)This function adds a role as an active role of a session whose owner is a given user.booleancheckAccess(Session session, Permission perm)Perform user RBAC authorization.SessioncreateSession(User user, boolean isTrusted)Perform user authentication User#password and role activations.voiddeleteSession(Session session)This function deletes a fortress session from the RBAC Policy Decision Point inside OpenLDAP RBAC Accelerator.voiddropActiveRole(Session session, UserRole role)This function deletes a role from the active role set of a session owned by a given user.List<Permission>sessionPermissions(Session session)This function returns the permissions of the session, i.e., the permissions assigned to its authorized roles.List<UserRole>sessionRoles(Session session)This function returns the active roles associated with a session.-
Methods inherited from interface org.apache.directory.fortress.core.Manageable
setAdmin, setContextId
-
-
-
-
Method Detail
-
createSession
Session createSession(User user, boolean isTrusted) throws SecurityException
Perform user authentication User#password and role activations.
This method must be called once per user prior to calling other methods within this class. The successful result isSessionthat contains target user's RBAC User#roles and Admin role User#adminRole.
In addition to checking user password validity it will apply configured password policy checks org.apache.directory.fortress.core.model.User#pwPolicy.
Method may also store parms passed in for audit trailFortEntity.This API will...
- authenticate user password if trusted == false.
- perform OpenLDAP password policy evaluation.
-
fail for any user who is locked by OpenLDAP's policies
User.isLocked(), regardless of trusted flag being set as parm on API. -
evaluate temporal
Constraint(s) onUser,UserRoleandUserAdminRoleentities. - process selective role activations into User RBAC Session User#roles.
-
check Dynamic Separation of Duties
DSDChecker.validate( org.apache.directory.fortress.core.model.Session, org.apache.directory.fortress.core.model.Constraint, org.apache.directory.fortress.core.util.time.Time, org.apache.directory.fortress.core.util.VUtil.ConstraintType)on org.apache.directory.fortress.core.model.User#roles. - process selective administrative role activations User#adminRoles.
-
return a
SessioncontainingSession.getUser(),Session.getRoles()and (if admin user)Session.getAdminRoles()if everything checks out good. - throw a checked exception that will be
SecurityExceptionor its derivation. - throw a
SecurityExceptionfor system failures. - throw a
PasswordExceptionfor authentication and password policy violations. - throw a
ValidationExceptionfor data validation errors. - throw a
FinderExceptionif User id not found.
The function is valid if and only if:
- the user is a member of the USERS data set
- the password is supplied (unless trusted).
- the (optional) active role set is a subset of the roles authorized for that user.
The following attributes may be set when calling this method
- @link User#userId - required
- org.apache.directory.fortress.core.model.User#password
- org.apache.directory.fortress.core.model.User#roles contains a list of RBAC role names authorized for user and targeted for activation within this session. Default is all authorized RBAC roles will be activated into this Session.
- org.apache.directory.fortress.core.model.User#adminRoles contains a list of Admin role names authorized for user and targeted for activation. Default is all authorized ARBAC roles will be activated into this Session.
- User#props collection of name value pairs collected on behalf of User during signon. For example hostname:myservername or ip:192.168.1.99
Notes:
- roles that violate Dynamic Separation of Duty Relationships will not be activated into session.
- role activations will proceed in same order as supplied to User entity setter, see User#setRole(String).
- Parameters:
user- Contains User#userId, org.apache.directory.fortress.core.model.User#password (optional ifisTrustedis 'true'), optional User#roles, optional org.apache.directory.fortress.core.model.User#adminRolesisTrusted- if true password is not required.- Returns:
- Session object will contain authentication result code
org.apache.directory.fortress.core.model.Session#errorId,
RBAC role activations
Session.getRoles(), Admin Role activationsSession.getAdminRoles(), OpenLDAP pw policy codes org.apache.directory.fortress.core.model.Session#warnings, org.apache.directory.fortress.core.model.Session#expirationSeconds, org.apache.directory.fortress.core.model.Session#graceLogins and more. - Throws:
SecurityException- in the event of data validation failure, security policy violation or DAO error.
-
deleteSession
void deleteSession(Session session) throws SecurityException
This function deletes a fortress session from the RBAC Policy Decision Point inside OpenLDAP RBAC Accelerator. The function is valid if and only if the session is a valid Fortress session.- Parameters:
session- object contains the user's returned RBAC session from the createSession method.- Throws:
SecurityException- is thrown if session invalid or system. error.
-
sessionRoles
List<UserRole> sessionRoles(Session session) throws SecurityException
This function returns the active roles associated with a session. The function is valid if and only if the session is a valid Fortress session.- Parameters:
session- object contains the user's returned RBAC session from the createSession method.- Returns:
- list containing all roles active in user's session. This will NOT contain inherited roles.
- Throws:
SecurityException- is thrown if session invalid or system. error.
-
checkAccess
boolean checkAccess(Session session, Permission perm) throws SecurityException
Perform user RBAC authorization. This function returns a Boolean value meaning whether the subject of a given session is allowed or not to perform a given operation on a given object. The function is valid if and only if the session is a valid Fortress session, the object is a member of the OBJS data set, and the operation is a member of the OPS data set. The session's subject has the permission to perform the operation on that object if and only if that permission is assigned to (at least) one of the session's active roles. This implementation will verify the roles or userId correspond to the subject's active roles are registered in the object's access control list.- Parameters:
perm- must contain the object, Permission#objName, and operation, Permission#opName, of permission User is trying to access.session- This object must be instantiated by callingAccessMgr.createSession(org.apache.directory.fortress.core.model.User, boolean)method before passing into the method. No variables need to be set by client after returned from createSession.- Returns:
- True if user has access, false otherwise.
- Throws:
SecurityException- in the event of data validation failure, security policy violation or DAO error.
-
sessionPermissions
List<Permission> sessionPermissions(Session session) throws SecurityException
This function returns the permissions of the session, i.e., the permissions assigned to its authorized roles. The function is valid if and only if the session is a valid Fortress session.- Parameters:
session- This object must be instantiated by callingAccessMgr.createSession(org.apache.directory.fortress.core.model.User, boolean)method before passing into the method. No variables need to be set by client after returned from createSession.- Returns:
- List<Permission> containing permissions (op, obj) active for user's session.
- Throws:
SecurityException- is thrown if runtime error occurs with system.
-
addActiveRole
void addActiveRole(Session session, UserRole role) throws SecurityException
This function adds a role as an active role of a session whose owner is a given user.The function is valid if and only if:
- the user is a member of the USERS data set
- the role is a member of the ROLES data set
- the role inclusion does not violate Dynamic Separation of Duty Relationships
- the session is a valid Fortress session
- the user is authorized to that role
- the session is owned by that user.
- Parameters:
session- object contains the user's returned RBAC session from the createSession method.role- object contains the role name, UserRole#name, to be activated into session.- Throws:
SecurityException- is thrown if user is not allowed to activate or runtime error occurs with system.
-
dropActiveRole
void dropActiveRole(Session session, UserRole role) throws SecurityException
This function deletes a role from the active role set of a session owned by a given user. The function is valid if and only if the user is a member of the USERS data set, the session object contains a valid Fortress session, the session is owned by the user, and the role is an active role of that session.- Parameters:
session- object contains the user's returned RBAC session from the createSession method.role- object contains the role name, org.apache.directory.fortress.core.model.UserRole#name, to be deactivated.- Throws:
SecurityException- is thrown if user is not allowed to deactivate or runtime error occurs with system.
-
-